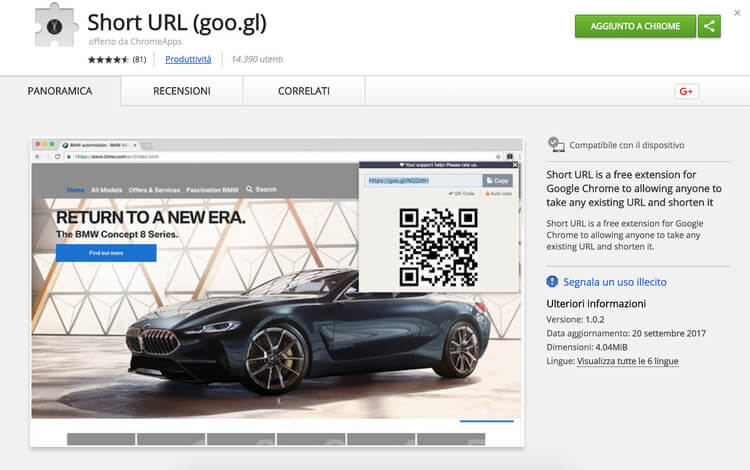
Monero is all the time utilized for criminal purposes, yet this doesn’t mean it is itself bad – it simply has great technological advancements that can be utilized by lawbreakers to conceal their tracks. That is why this special Google Chrome plugin intended for URL shortening (such as TinyURL in mechanics), was infected with Coinhive, a script that mines Monero.
For this situation, we owe our appreciation to Alessandro Polidori, a very much talented programmer who effectively figured out how to discover the threat source after getting a warning from Intrusion Prevention System composed by Nethserver.
In the event that you don’t have decent detection tools, latent in-browser mining can be killed by reinstalling the browser or essentially shutting the website page that gets too much resources of your PC (this can be checked from the Task Manager in we talk about Windows). Soon, major antiviruses will figure out how to battle this threat even more effectively, but for now, it’s better to follow the news about latent miners and malvertising – a process when a good website is injected with a cryptocurrency mining malware and therefore turns into the hackers’ tool of stealing resources.
– Follow us on our Facebook and Twitter pages.