The software and hardware technology company of Microsoft has removed 8 malicious crypto jacking apps from the Microsoft Store. This was after the team at Symantic notified the firm of the existence of the free apps that were using user’s CPU power to mine Monero (XMR). Symantic notified Microsoft of the malicious apps on the 17th of January. The removal of the apps was confirmed via a blog post earlier today that stated the following:
On January 17, [Symantic] discovered several potentially unwanted applications (PUAs) on the Microsoft Store that surreptitiously use the victim’s CPU power to mine cryptocurrency. We reported these apps to Microsoft and they subsequently removed them from their store.
Hiding in Plain Sight
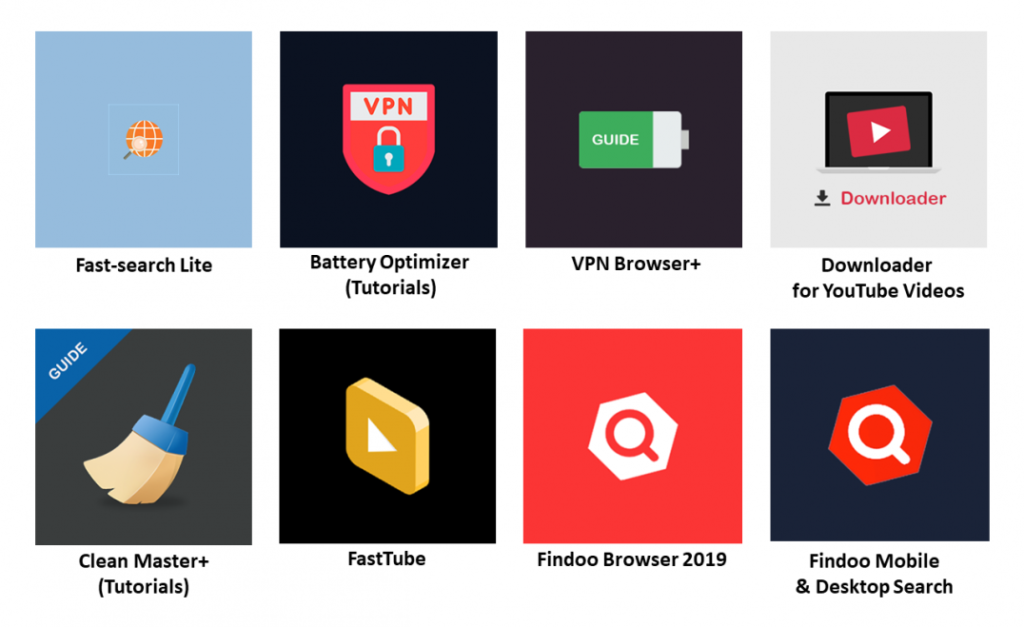
The blog post went on to explain that the apps included those for computer and battery optimization tutorial, internet search, web browsers, and video viewing and download. All the 8 apps came from three developers: DigiDream, 1clean, and Findoo. Symantic went on to postulate that the three developers are probably linked to the same person/group. The apps were published between April and December 2018.
The eight apps included:
- Fast-search Lite
- Batter Optimizer (Tutorials)
- VPN Browser+
- Downloader for YouTube Videos
- Clean Master+ (Tutorials)
- FastTube
- Findoo Browser
- Findoo Mobile and Desktop Search
 Despite the apps being available for a short time period, a significant number of users might have downloaded them. Users might have been lured into installing them through the top free apps list on the Microsoft Store or by searching for apps that provide a certain type of service. The apps had also received 1,900 ratings that might have added to their legitimacy for download.
Despite the apps being available for a short time period, a significant number of users might have downloaded them. Users might have been lured into installing them through the top free apps list on the Microsoft Store or by searching for apps that provide a certain type of service. The apps had also received 1,900 ratings that might have added to their legitimacy for download.
Utilizing the CPU to Mine Monero
Symantic summed up how the apps managed to access machines to mine Monero.
As soon as the apps are downloaded and launched, they fetch a coin-mining JavaScript library by triggering Google Tag Manager (GTM) in their domain servers.
The mining script then gets activated and begins using the majority of the computer’s CPU cycles to mine Monero for the operators. Although these apps appear to provide privacy policies, there is no mention of coin mining on their descriptions on the app store.
What are your thoughts on the proliferation of malicious apps that end up crypto-jacking computers and smartphones? How can such innovation be tapped for the greater good of the crypto and blockchain industry? Please share your ideas in the comment section below.
[Feature image courtesy of Unsplash.com]
Disclaimer: This article is not meant to give financial advice. Any additional opinion herein is purely the author’s and does not represent the opinion of Ethereum World News or any of its other writers. Please carry out your own research before investing in any of the numerous cryptocurrencies available. Thank you.