Suspected hackers have successfully managed to attack another cryptocurrency project, this time, KickICO. The attackers were able to steal 70 million KICK which has a market value of about $7.7 million. The hack comes barely two weeks after Bancor, a decentralized exchange platform suffered a $23.5 million cyberattack.
Details of the Hack
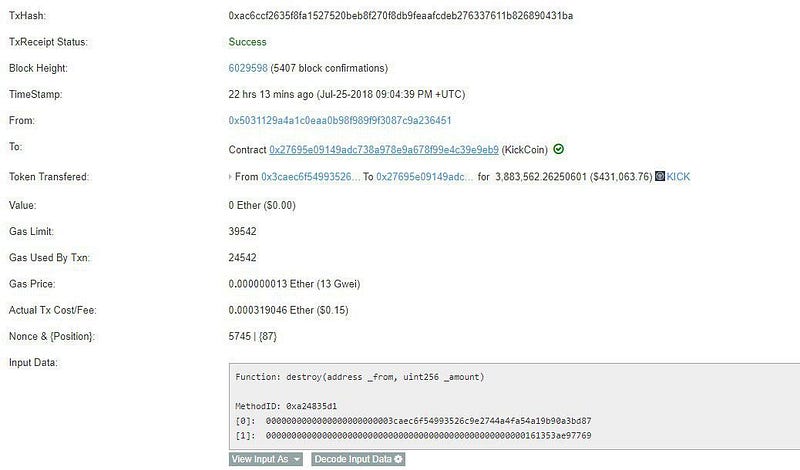
According to a statement released via the project’s Medium page, the attack occurred at 9:04 UTC, yesterday (July 26, 2018). The suspected attackers gained control of the project’s smart contract by obtaining a private key, thus, allowing them to siphon coins from the wallet of users.
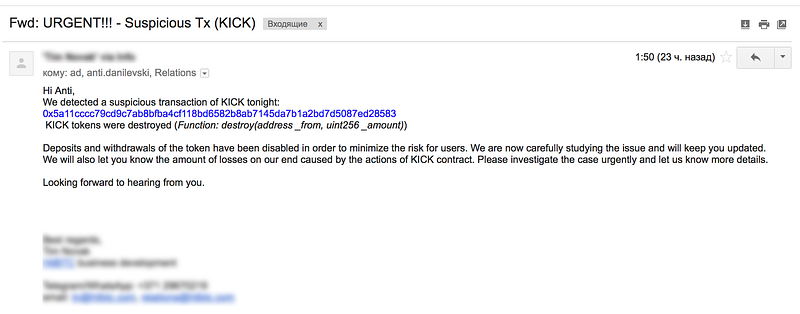
With full access to the project’s smart contract, the hackers were able to replace 40 different addresses with new spoof addresses containing the same amount of KICK tokens. By so doing, the hackers didn’t alter the total supply of KICK tokens hoping that such a tact would enable them to fly under the radar.
Only the timely intervention of the project team prevented the attack from being more catastrophic. Once alerted to the situation, the project team was able to arrest the situation by replacing the compromised key with a that of the cold storage wallet. The announcement also advised users who lost funds in the attack to send an email to the project team.
Plans to Reimburse Affected KickICO Users
The announcement also revealed that affected users would be reimbursed, saying:
We’ll return [sic] exact amount of tokens to their legit owners. We apologize for the inconveniences but guarantee that the situation is under control.
The working theory of the internal investigators on the attack is that the recent price growth of KICK tokens caused the project to become a potential target of hackers. In the past fortnight, KICK coins rose from $0.4 to 0.12. However, it is disconcerting to note that the attack took place only because the hackers got access to a private key.
What do you think about the KickICO hack? Keep the conversation going in the comment section below.
Image courtesy of Medium (KICKICO OFFICIAL).